How to do a ZipCrypto plaintext attack
Page Status: Finished (What's this?)
Summary¶
This post describes the Biham and Kocher plaintext attack on an encrypted ZIP file that uses the ZipCrypto Store encryption method. Also, don't use the ZipCrypto encryption to send confidential files, use AES256 instead.
Introduction¶
Let's imagine the following purely fictional scenario:
- Due to remote learning, you have to take your exams online.
- Your high school teacher or university professor hands out the exam file a couple days in advance, so that people with a slow internet connection don't have a disadvantage.
- To prevent students from peeking into the exam, they encrypt the ZIP file with a password that is handed out when the test begins.
You might be wondering: Is there any way to bypass this encryption? Just out of curiosity. You can try bruteforcing all possible password combinations, but that may take a long time. However, if the ZIP file is encrypted with the ZipCrypto Store algorithm, you can attempt a known-plaintext attack.
Important
Only attempt this attack to ZIP archives that you have created yourself. I am not responsible for any damages or legal issues you cause.
Prerequisites¶
You need the following things for the attack:
- The bkcrack program from its GitHub repository.
- The encrypted ZIP file with top secret contents.
- 8-12 bytes of known information about the stored file.
- A ZIP program. I used 7zip.
- A hexadecimal editor. I used HxD.
Check that the used encryption method is ZipCrypto Store. In 7zip, open the encrypted ZIP file, right click on the PDF file and click on "Properties":
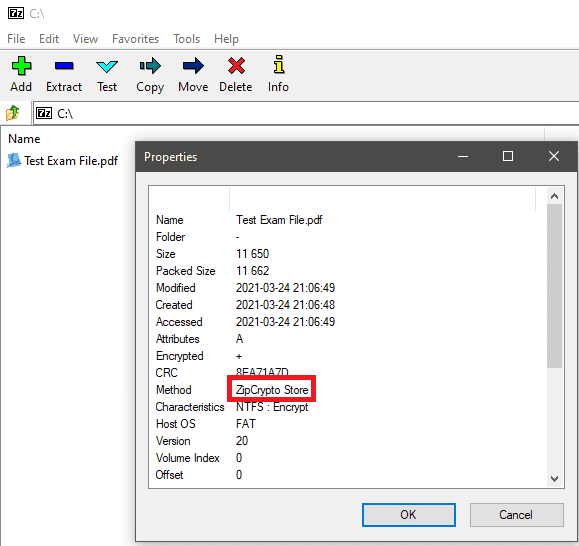
IMPORTANT REQUIREMENT
- If AES256 was used to encrypt the file, you can't use this form of plaintext attack.
- If ZipCrypto Deflate was used, it is much harder to execute the attack. You can go to the last chapter "The problem with ZipCrypto Deflate" if you want to learn more.
Executing the plaintext attack¶
After you've confirmed that the file was encrypted with ZipCrypto Store, do the following:
- Create a file to store your plaintext bytes, for example
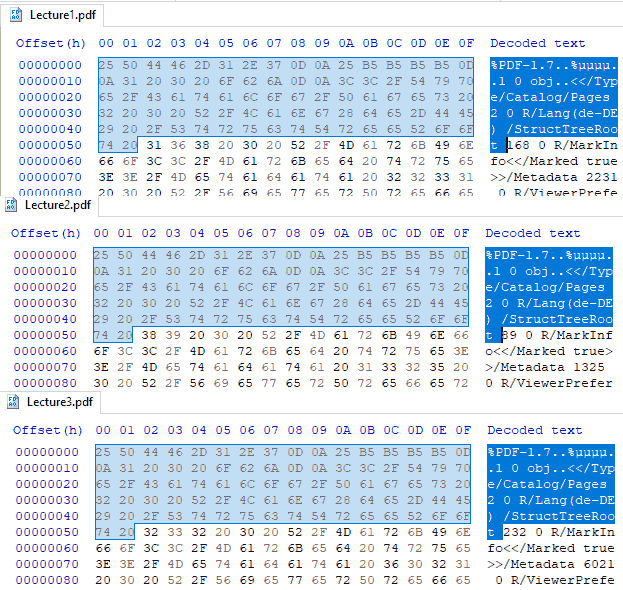
plain.bin - Open the PDF files from your lecture in the hex editor.
- Analyze the first bytes of each PDF file to identify as many matching bytes as you can:
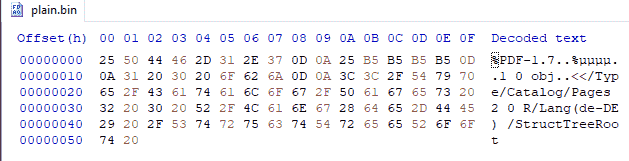
After you identified the plaintext bytes:
- Insert them into your plaintext file:
- Copy your plaintext file and encrypted ZIP file to the folder where bkcrack.exe is located
- Execute the following command in the command line:
If the attack was successful, the program outputs three keys that you can use to decrypt the files:
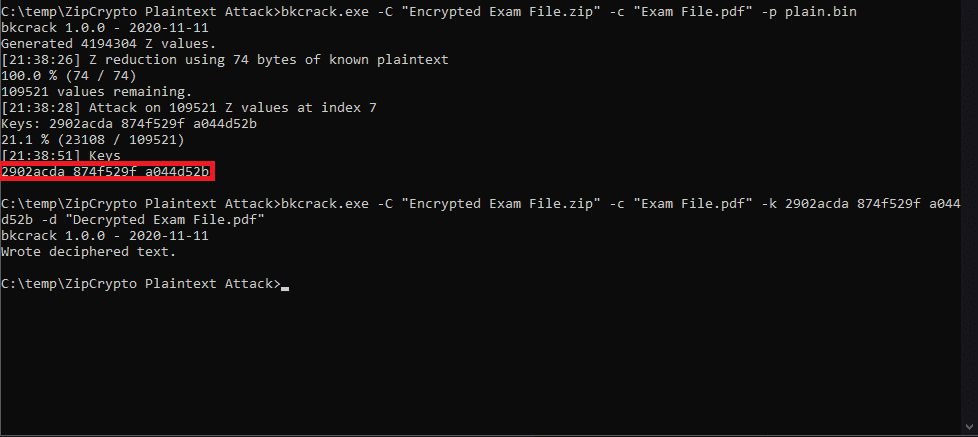
Decrypt the files with the following command:
bkcrack.exe -C "Encrypted Exam File.zip" \
-c "Exam File.pdf" \
-k [Your] [Keys] [Here] \
-d "Decrypted Exam File.pdf"
And done! You have successfully decrypted the file.
How to prevent this attack¶
Plaintext attack prevention
Use AES256 encryption.
The problem with ZipCrypto Deflate¶
(Update from 2022-12-18)
When the ZIP archive was created with Deflate, the files are compressed before storing them in the ZIP file. Because of this, you are unable to use your known bytes for the files, as the compression "scrambles" or "mixes up" the whole file.
However, it is not impossible to extract the password: If the archive contains multiple files and you have an exact copy of one of them, you can still try the plaintext attack. Examples for such files are:
- DLLs
- License notices (Like MIT, GPLv3) where the contents weren't changed
- Company logos / icons, other widely used pictures
When you have a file like this, you can do the following:
kimci86 (source)
Then, one would compress it using various compression software and compression levels to try and generate the correct plaintext.
So you would have to repeat the following steps with different compression strength (low-high):
- Compress your known file with the DEFLATE algorithm (e.g. by using a CLI tool)
- Use the first bytes (or the whole file) of your compressed files as the known bytes for the attack
- Execute the attack
- If that didn't work: use the next compression strength
This means that ZipCrypto Deflate is much more tedious than ZipCrypto Store.